In this article, we’re going to talk about Distributed Denial of Service or DDoS Attack.
A Denial of Service Attack is a type of attack where the attacker sends packets to a server until the server dies or stops responding.
In the Distributed Denial of Service(DDoS) attack, not only one computer but lots of computer around the world sends packets and data to a server in this way server can’t handle too many requests and it results in crashing of the server.
These type of attacks basically takes advantage of the limits of requests server can handle and send more than that, DDoS attacks are very very dangerous even a small scale DDoS attack can cause a server huge amount of damage. Therefore It’s recommended do not to try this on any network without permission.
If you want to try DDoS attack try on your own network or website to see how its working.
How DDoS attack Works?
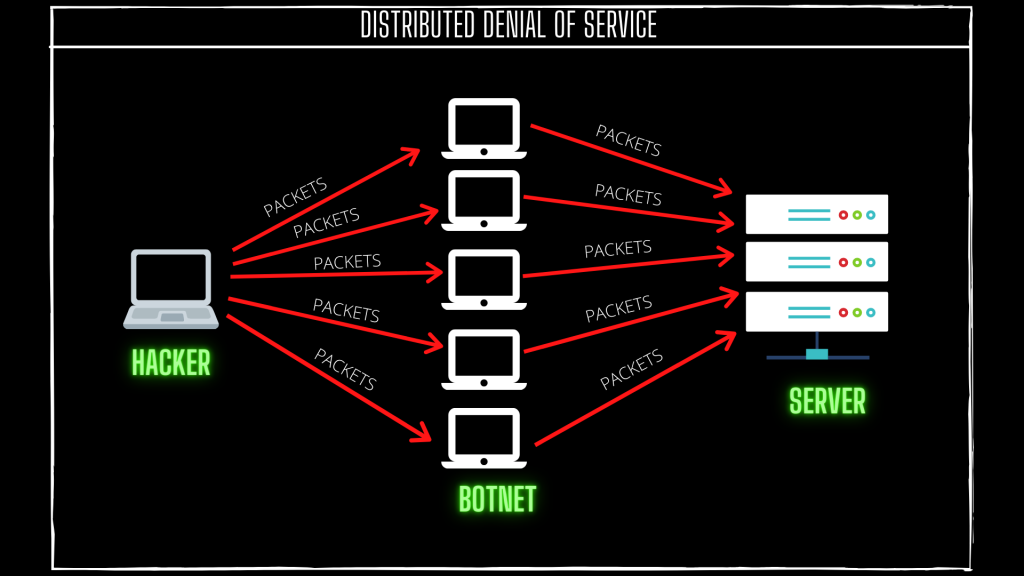
This is exactly how a DDoS attack works
DDos contains three major components an attacker, a botnet, the target server.
What is Botnet?
A botnet is a network of computer which are under the control of the hacker, and he can do almost anything from those compromised computers.
The attacker sends a command to run a DDoS script or exploit to the botnets, scripts which are directed to send packages of data to a specific server.
The Server can’t handle that much traffic and it results in crashing of the server.
How to do DDoS Attack?
(ONLY FOR EDUCATIONAL PURPOSE)
There are many ways of doing a DDoS attack try them on your server or website never try them on other websites.
1.)Low Orbit Ion Cannon (LOIC)
Low Orbit Ion Canon is a software that can perform a small scale DDoS attack on server. But its still dangerous a small scale DDoS can also cause very much damage.
There is a lack of anonymity in LOIC it’s easily traceable.
Link->https://sourceforge.net/projects/loic/
2.)High Orbit Ion Cannon(HOIC)
It is a free denial of service tool, and is designed to attack more websites at once. you can attack upto 256 website at once.and also you can control your attack to low medium or high setting. This tool uses http protocols to do a DDoS attack
Link-> https://sourceforge.net/projects/highorbitioncannon/
3.)HTTP Unbearable Load King(HULK)
This tool is best for generating volumes of traffic and send it to web servers. It creates unique network traffic and can easily bypass the cache server.
Link->https://packetstormsecurity.com/files/112856/HULK-Http-Unbearable-Load-King.html
4.)Tor’s Hammer
Tor’s hammer is a slow rate HTTP post-DoS tool. It automatically converts the URL to links. This tool is difficult to track because it launches the attack from random Source IP addresses which makes tracking the attacker almost impossible.
Link->https://sourceforge.net/projects/torshammer/
All these tools can be used to perform DDoS or DoS attacks and there are a lot of tools and scripts that you can use to perform a DDoS.
Performing DDoS is simple and yet very dangerous.
If you want to checkout some more DDoS tools click here.