Encryption, encoding and hashing, these terms are commonly interchanged and used incorrectly. They are kind of similar terms and are often confused with each other.
Let’s Discuss them One-by-One.
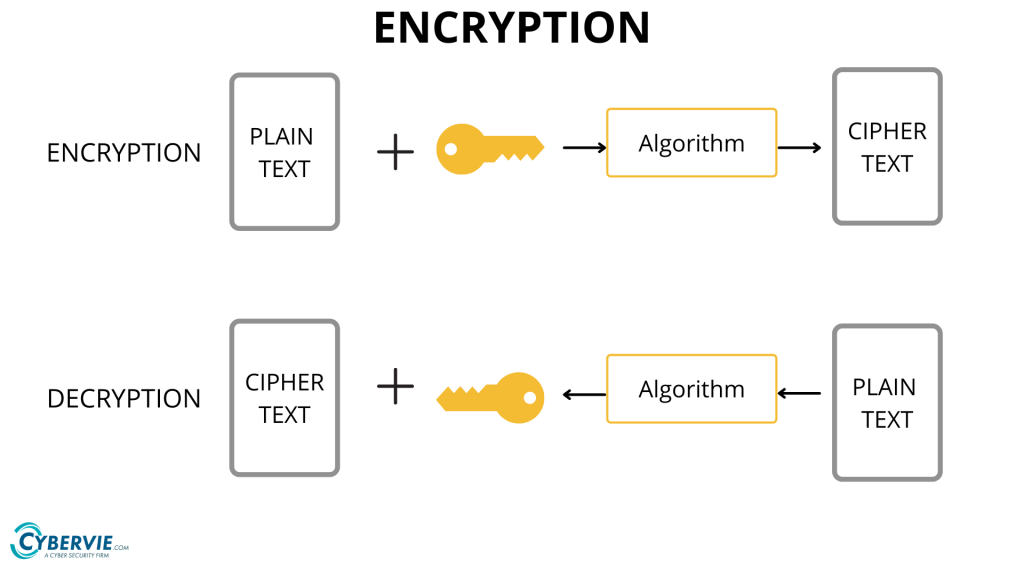
Encryption
Encryption is the process of securely encoding data in such a way that only authorized users with a key or password can decrypt the data to reveal the original.
The process ensures that the intended recipient receives the transmitted data. It is a special type of encoding that is used for transferring private data, for example sending a combination of username and password over the internet for email login.
In encryption, data to be encrypted(called plain-text) is transformed using an encryption algorithm like AES encryption or RSA encryption using a secret key called a cipher.
The encrypted data is called cipher-text, and finally, the secret key can be used by the intended recipient to convert it back to plain text.
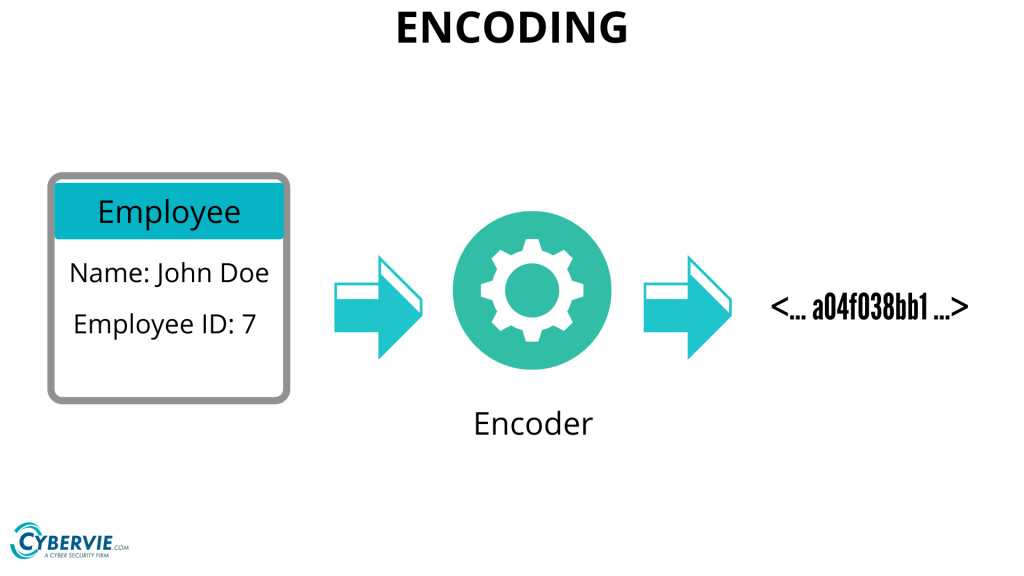
Encoding
In the Encoding method, data is transformed from one form to another. So, that it can easily restore back into the predefined data. It does not need any key to decode it.
Encoding data is typically used to ensure integrity and usability of data and is commonly used when data cannot be transferred in its current format between systems or applications.
Encoding transforms data into another format using a scheme that is publicly available so that it can easily be reversed.
Examples: ascii, unicode, URL Encoding, base64.
Encoding can be used for reducing the size of audio and video files.
Hashing
Hashing is converting a string of characters such as letters, numerals or symbols by applying a mathematical formula.
In hashing, data is converted to the hash using some hashing function, which can be any number generated from string or text. Various hashing algorithms are MD5, SHA256. Data once hashed is non-reversible.
In contrast to encoding, hashing cannot be reversed. It is not possible to take a hash and convert it back to the original data without hashing key. Hashing is commonly used to verify the integrity of data.
There are also other hashing uses, including the hash functions of modern day cryptography. Here are some of these applications:
- Message Digest
- Password Verification
- Data Structures
- Compiler Operation
- Rabin-Karp Algorithm
- Linking File name and path together
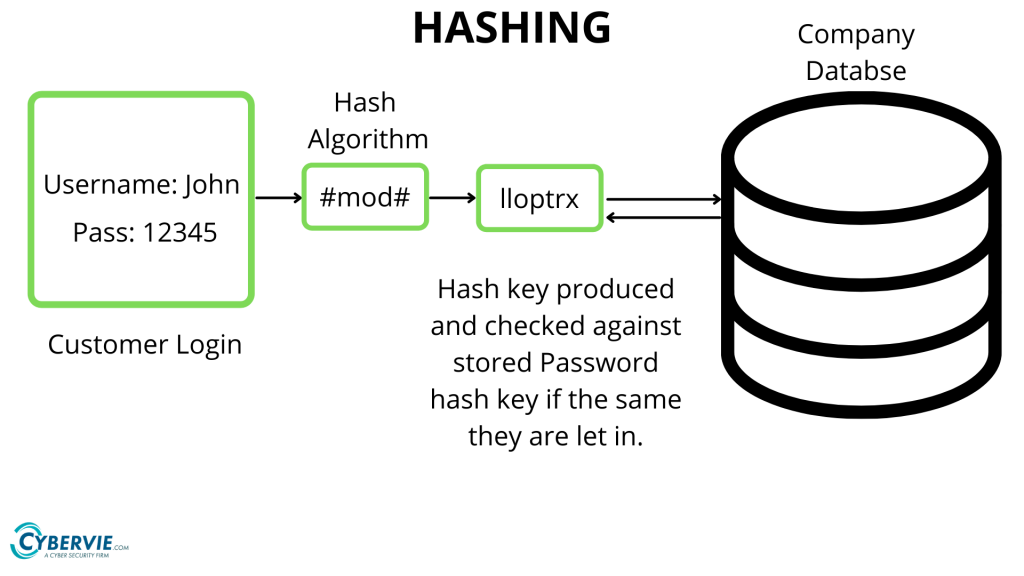
Another purpose for hashing is for verifying passwords for login on various websites, as shown in the image.