The first question that comes is, What is it?
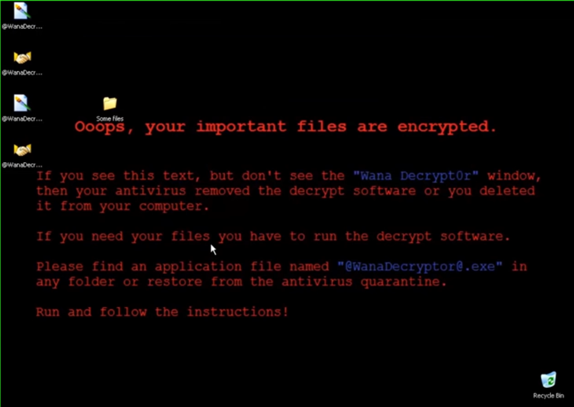
A worm is known as WannaCrypt, Wana Decrypt0r 2.0, WanaCrypt0r 2.0, and Wanna Decryptor, with many names the functionality remains the same ransomware following its basic principle “Encrypt Files and Demand Ransom”.
Some Details about the Attack
- The attack took place on 11th May, 2017. It was considered to be a network worm as it required some transport mechanism to propagate further. It targeted computers that ran Microsoft Windows operating system by encrypting all the data present on the system and demanding ransom payments in the Bitcoin cryptocurrency.
- The WannaCry ransomware attack hit around 230,000 computers globally. One of the first companies affected was the Spanish mobile company, Telefónica. By May 12th, thousands of NHS hospitals and surgeries across the UK were affected. As the ransomware spread beyond Europe, computer systems in 150 countries were crippled.
- The WannaCry ransomware attack had a substantial financial impact worldwide. It is estimated this cybercrime caused $4 billion in losses across the globe.

How did it happen?
All of this happened through EternalBlue, an exploit developed by the United States National Security Agency (NSA) for older Windows systems. After having taken access of the machine and encrypting the files, the payload displayed a message informing the user that files have been encrypted, and demanding a payment of around US$300 in bitcoin within three days, or US$600 within seven days, warning that “you have not so enough time.” Three hardcoded bitcoin addresses, or wallets, are used to receive the payments of victims. Although the transactions and balances of the wallet were publicly accessible even though the cryptocurrency wallet owners remain unknown. When executed, the WannaCry malware did an initial check for the kill switch domain name, if it was not found, then the ransomware would encrypt the computer’s data, then attempts to exploit the SMB vulnerability to spread out to random computers on the Internet, and laterally to computers on the same network.

EternalBlue was stolen from the NSA and leaked by a group called The Shadow Brokers at least a year before the attack. The NSA had already discovered the vulnerability but used it to create an exploit for its own offensive work, rather than report it to Microsoft.
Tackling the mess
Microsoft eventually discovered the vulnerability, and on Tuesday, 14 March 2017, they issued security bulletin MS17-010, which detailed the flaw and announced that patches had been released for all Windows versions that were currently supported at that time, which comprised of Windows Vista, Windows 7, Windows 8.1, Windows 10, Windows Server 2008, Windows Server 2008 R2, Windows Server 2012, and Windows Server 2016.
While Microsoft had released patches previously to close the exploit, much of WannaCry’s spread was from organizations that had not applied these or were using older Windows systems that were past their end-of-life. These patches are imperative to an organization’s cyber-security but many were not applied because of needing 24/7 operation, risking having applications that used to work break, inconvenience, or other reasons.

Defense:
A Kaspersky Lab study reported, however, that less than 0.1 percent of the affected computers were running Windows XP, and that 98 percent of the affected computers were running Windows 7.
The attack was halted within a few days of its discovery due to emergency patches released by Microsoft. Although Microsoft quickly issued a patch for WannaCry, not every organization could roll it out quickly enough. In fact, some customers were using a version of Windows so outdated that the patch couldn’t even be applied. Another breakthrough that saved millions of devices was the discovery of a kill switch by Marcus Hutchins that prevented infected computers from spreading WannaCry further. The attack was estimated to have affected more than 200,000 computers across 150 countries, with total damages ranging from hundreds of millions to billions of dollars. Security experts believed from preliminary evaluation of the worm that the attack originated from North Korea or agencies working for the country. In December 2017, the US and UK formally asserted that the attack was from North Korea.
After Effects
A new variant of WannaCry forced Taiwan Semiconductor Manufacturing Company (TSMC) to temporarily shut down several of its chip-fabrication factories in August 2018. The virus spread to 10,000 machines in TSMC’s most advanced facilities.

Also, See about the REvil Ransomware.
For more blogs like this please visit our blog page