Cybersecurity Interview Questions Part-4

In continuation of our interview series, here we are presenting the 4th part in our interview series. Let’s begin: Q1. How firewall can aid in malware mitigation? An enterprise firewall between your internal network and the Internet provides one layer of protection for the internal computers. However, not all threats come through the “front door” […]
Cybersecurity Interview Questions Part-3

In the continuation of our interview questions series, here we present the next part of our interview questions, Lets begin: Q1. Name some malware identification tools. Some of the mostly used tools in identification of malware is: CrowdStrike Falcon Insight EDITOR’S CHOICE This EDR analyzes malware on two levels and also identifies intruder activity. The […]
Linux File System
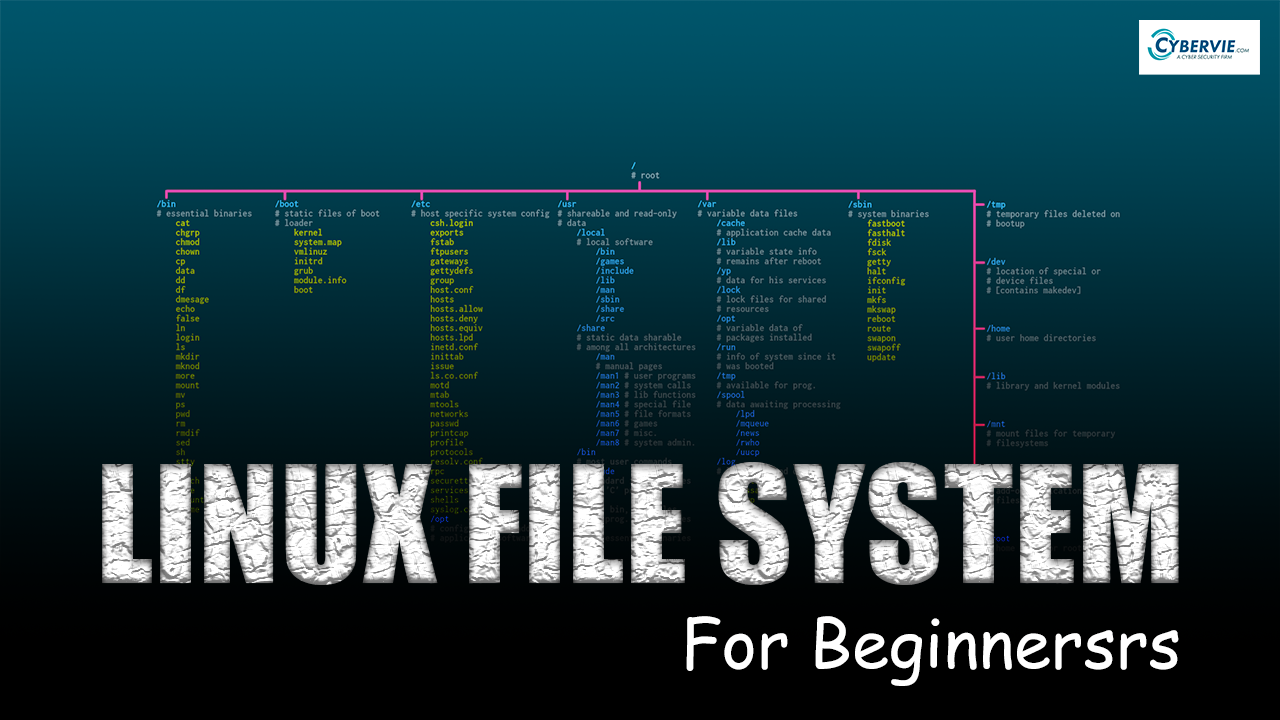
Linux File System If you are in IT Field or thinking of getting into it. Then a deep understanding of Linux is very important. In this article, we are going to get a decent understanding of Linux File System. What is a File System ? OS stores data on disk drives using a structure called […]
Cybersecurity Interview Questions: 2

In the continuation of our Interview Question Series, we are publishing our second part of total five series. In this part we will be briefly seeing the Interview Questions for cybersecurity from the perspective of malware, a most common threat, almost encountered in each event and still a preferred choice for various APT groups. Let’s […]
How a Cybersecurity Career Can Actually Secure Your Future

Want to know what you can achieve with cybersecurity as a career for you? Take a quick look into how training in cybersecurity can secure your life!
Here’s Your One-Stop Guide to Everything About Cybersecurity

Intelligent cloud security solutions keep customer data protected while embracing new technology. There is an increasing reliance on next-generation technology in this world. The best strategy to protect customer data is impenetrable strategies. This prevents unauthorized access. And that’s right where the application of cybersecurity comes in. ALL ABOUT CYBERSECURITY Cybersecurity is the practice of […]


