- info@cybervie.com
- +91-9000878798
- Live Support
Software Exploitation Attacks can be used to gain access to unauthorized systems, leverage user account privileges, crash systems or provide installation of malicious software (such as Spyware, Virus’s, Trojans, Adware, etc.) without the awareness of the other party. Metasploit is a very popular tool to launch such attacks. Before learning about Metasploit, let us see what are the attack vectors employed by attackers and the meaning of an exploit.

Gaining access to a secured system can be a difficult task that requires skill and maybe luck. However, we have also have plenty of simple techniques, commonly used today, to achieve the same result. Such include:
Eg:Wireless Routers have default passwords
Eg: Windows Administrator Account are often blank
2. Password Brute Force Attack
These methods have become extremely fast with the of Rainbow Tables!(Rainbow tables pre-computed tables of password hashes.)
Ex: Phishing Attacks
2. A malicious user who impersonates him or herself as trustworthy a entity
Ex: Injection of SQL to spit out information from certain tables
Ex: Inject an administrator account for yourself
Out of all the methods discussed above, one of the most dangerous and yet a very effective attack used by malicious users today are Software Exploitation Attacks!
Every software has certain vulnerabilities or weaknesses in the system that allow an attacker to violate the integrity, confidentiality, access control,consistency or the data and applications that the particular software hosts. For a software developer, a bug is synonymous to a vulnerability. That is it usually implies errors in program’s source code or flawed program design.
Examples:
Regardless though which type of software bug we are speaking of, they are used as the foundation to form an exploit.Therefore, an exploit is a security attack on a vulnerability.
In other words, an exploit attacking a vulnerability is generating an event that the application/program/OS is not programmed/designed to recover successfully and therefore the result is a system that discontinues to function correctly.Software providers will, of course, issue security patches for all the vulnerabilities they come to know about, but until they do, the software could be at risk.
According to the Metasploit Team: “The Metasploit Framework is a platform for writing, testing, and using exploit code. The primary users of the Framework are professionals performing penetration testing, shellcode development, and vulnerability research.”
The Metasploit Framework (MSF) provides the ability to launch exploits against selected target systems, and to perform post-exploitation tasks, such as uploading files, running processes, establishing backdoor network connections, monitoring system use, and many more. Therefore, its primary use is in the penetration testing process.Another important use of the MSF is in systems administration.
MSF is not only an environment for exploit development but also a platform for launching exploits on real-world applications. It is packaged with real exploits that can provide real damage if not used professionally. The fact that MSF is an open-source tool and provides such a simplified method for implementing dangerous attacks, it has and still is attracting wannabe hackers that do no more than create additional problems on networks and system.
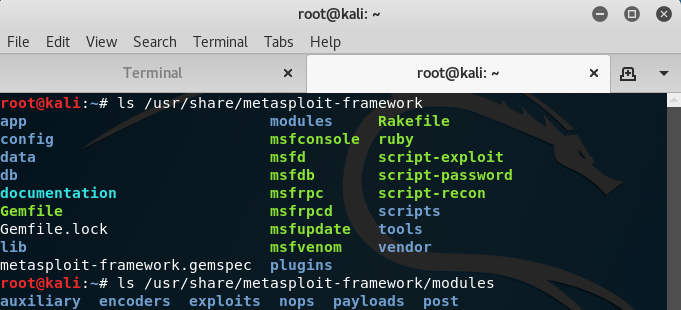
MSF has 6 types of modules as follows:
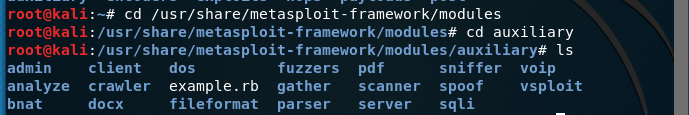
Auxiliary modules do not require the use of a payload to run like exploit modules. These types of modules include useful programs such as scanners, fuzzier, and SQL injection tools.
The victim application or the transmission protocol may be resistent to the exploit code and may break it up into several pieces which is undesirable. It is the encoders job to ensure that the playloads make it to their destination in one piece without any disruption.

Exploit modules are pieces of code within the database that when running on a victim computer. The attacker will attempt to leverage a vulnerability on the local or remote system endangering the payload module such as Meterpreter shell.

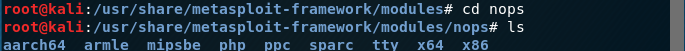
In low level language (assembly language), NOP is short for No Operation. At the point when a processor stacks that instruction, it basically does nothing (in any event helpful) for the one cycle and afterward progresses the register to the next instruction.
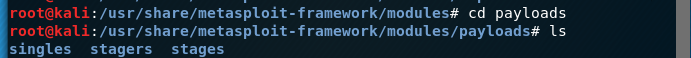
While using an exploit against a vulnerable machine, a payload is generally attached to the exploit before its execution. The payload contains the set of instructions that the victim’s computer is to carry out after compromise. It can range from a few lines of code to a small application.
Metasploit post exploits modules permit penetration tester to collect data from compromised machines, including hashes, tokens, provision passwords and a great deal more.

Metasploit contains over 1.500 different exploits and new ones are added regularly. With this vast number of exploit the search function, and knowing how to use it, becomes very important. The easiest way of using the search function is by issuing the command search followed by a search term.
Example: If I want to search for win8 attack payloads, I’ll simply start metasploit and type search win8

2. Help and info
The help command will return a list of possible commands together with a description when typed at the msfconsole.
For a paprticular exploit, we can retrieve information like the name, platform, author, available targets and a lot more by using the info command.

3. Use
The use command in Metasploit is used to activate a particular module and changes the context of the msfconsole to that particular module.
![]()
4. Show and set
The show options command will show you the available parameters for an exploit if used when the command line is in exploit context.
You can use the set command to change the default values for the option names returned. example: SET RHOST 92.168.0.1

When all the required options have been set for the exploit, including a payload and advanced settings like a NOP generator, evasion options and encoding, the exploit is ready to be executed. The exploit can be executed using two commands: run and exploit. Just type run or exploit in the msfconsole and the exploit will run.
This guide has introduced the Metasploit Framework including it’s modules and basic commands which is a widely used exploitation tool by professionals in the security industry due to it’s various extensible features.