Detecting against PID Spoofing
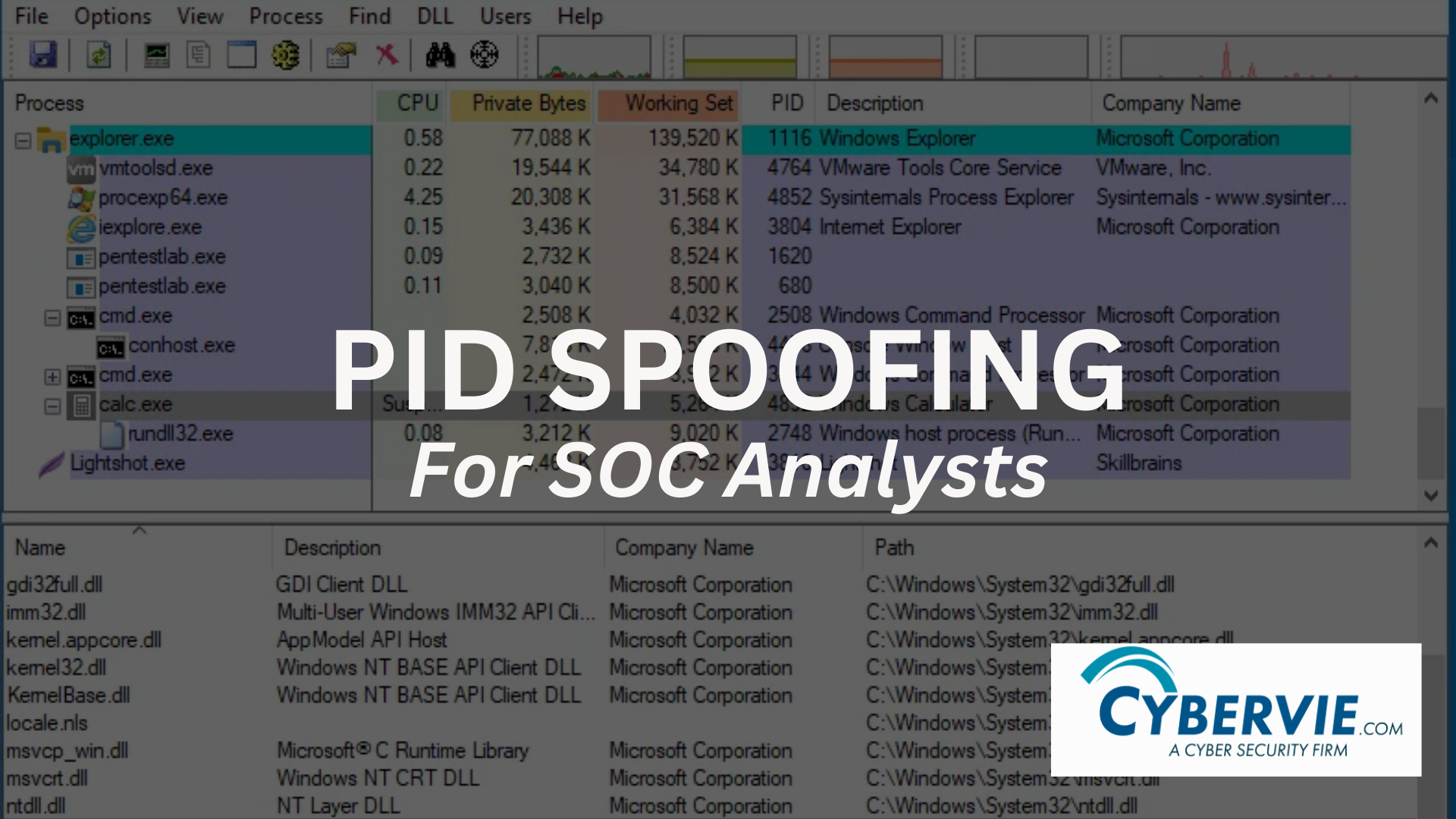
Defending against PID Spoofing In the ever-evolving landscape of cybersecurity, identifying and thwarting sophisticated threats like PID (Process ID) spoofing is paramount. This blog delves into the intricacies of detecting PID spoofing in Windows systems, offering comprehensive strategies and insights from a Blue Team perspective. To defend you must know how it works, for […]


