Essential Cyber Security Concepts

Man-In-The-Middle Attacks|Different Types and Techniques
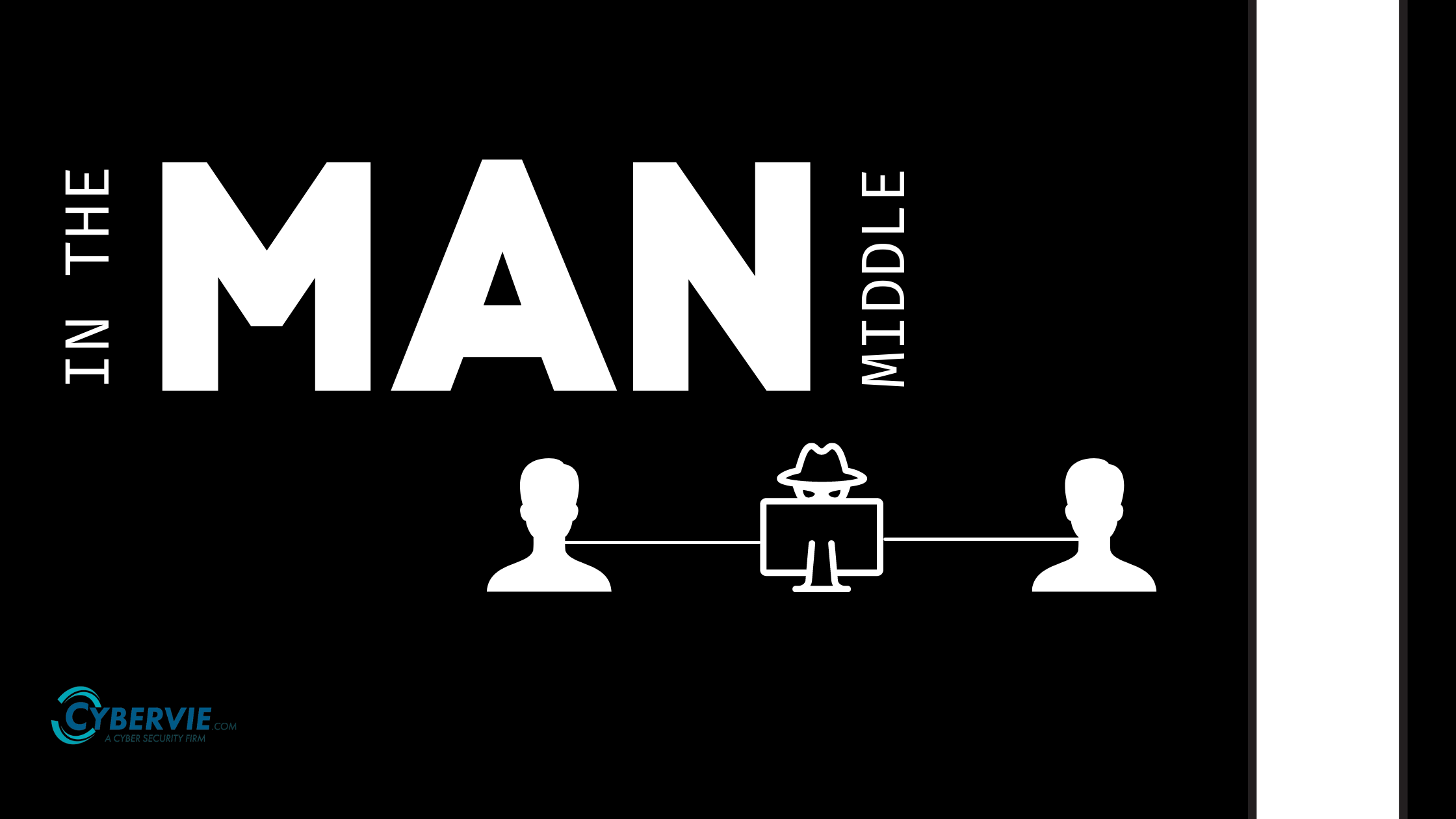
In this article we are going to see about Man In the middle attack and types of MITM attacks

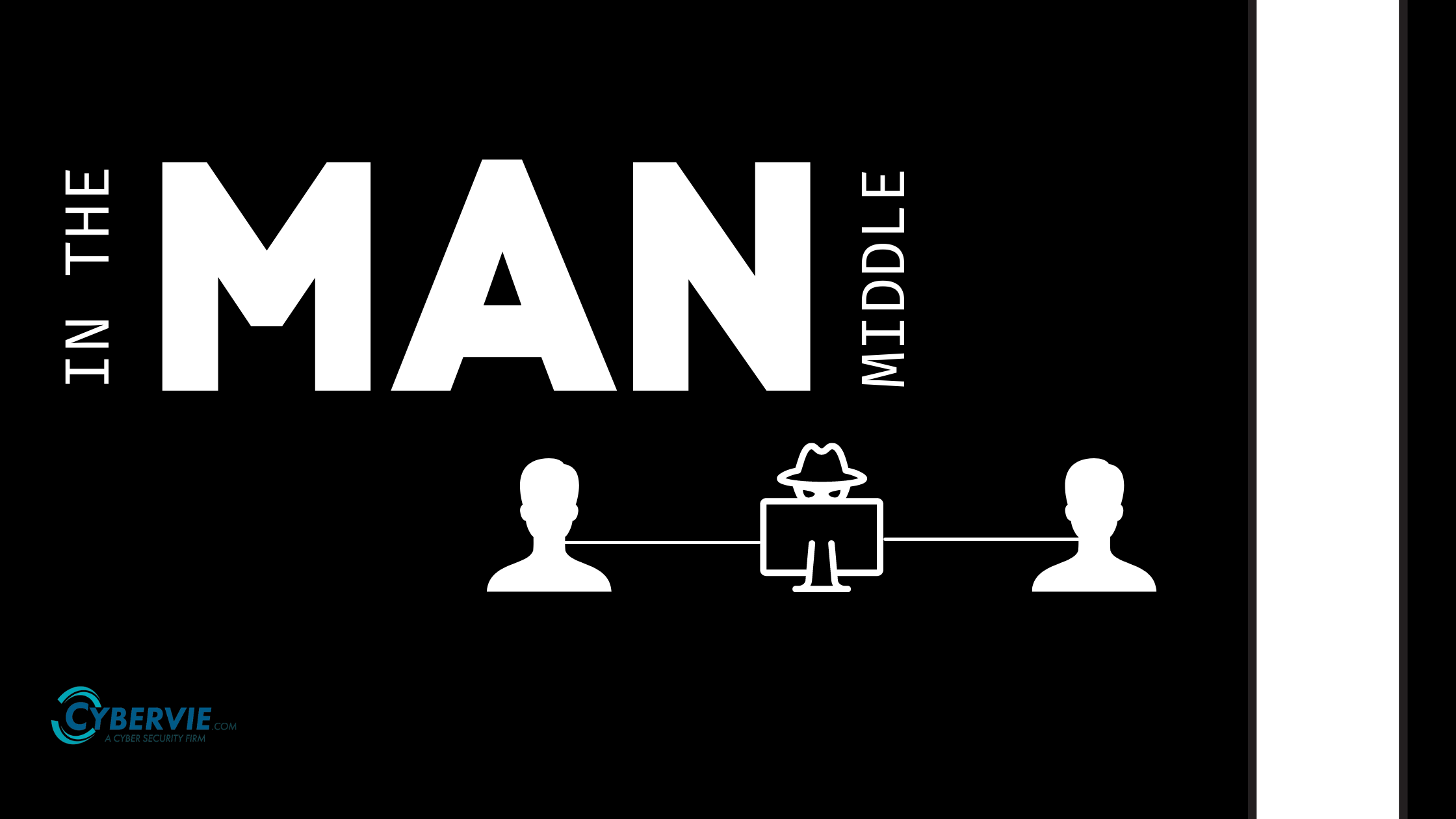
In this article we are going to see about Man In the middle attack and types of MITM attacks

© 2024 Ionots Technologies Pvt.Ltd | All Rights Reserved.
© 2024 Ionots Technologies Pvt.Ltd | All Rights Reserved. | Created By Mohit Goyal