Cisco is one of the leading companies in the IT and Networking sector. A few days back Cisco faced a massive cyber attack by a group of hackers. More than 200,000 network switches belonging to the company were hacked. Many countries were affected including Iran, Russia, United States, China, and India. The data loss and the impact are not completely evident yet.
The Target:
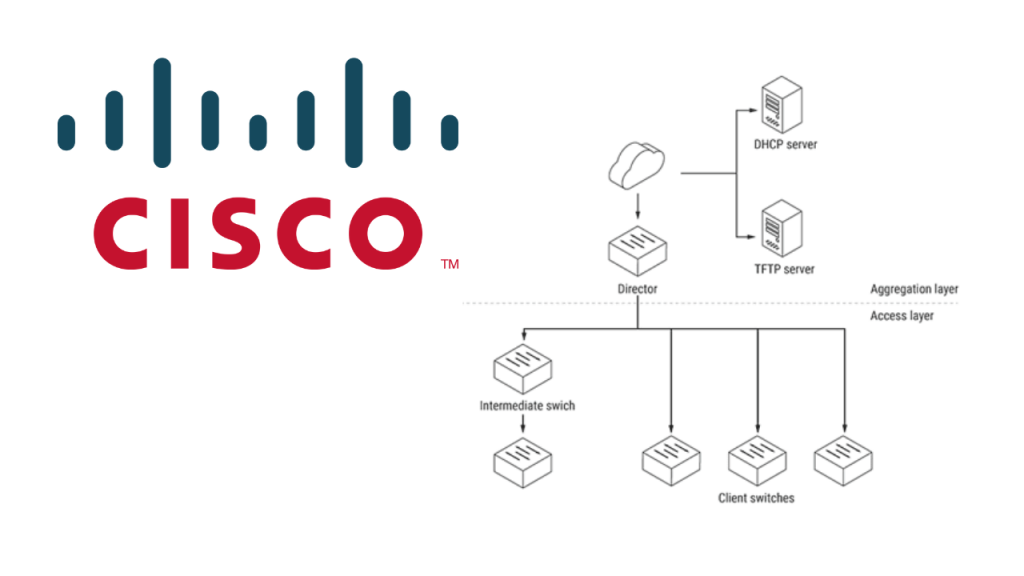
The attack affected 200,000 router switches all around the world. The attack exploited a vulnerability in software called Cisco Smart Install Client. This allows hackers to run arbitrary code on the vulnerable switches, according to a blog by Kaspersky Lab. The targeted devices were reset and they became unavailable for configuration. As a result, this attack affected internet service providers and data centres. The web subscribers’ internet connections were cut off due to this flaw in the routers.
This vulnerability has given access to the inner system infrastructures to the hackers. Therefore the data in the data centres may be in jeopardy. The vulnerable data may lead up to many more cyber crimes like intellectual property theft, identity theft etc. Though there has been no sign of such crimes yet, it may be wise to be aware of such attacks in case there is a crisis in the future.
The Vulnerabilities:
It has been seen that there are quite a few other vulnerabilities that can be exploited to change the configuration of the router and attack it with malicious code. They can gain control and execute random code on the victim’s router. This can also lead to denial of service conditions.
Safety Measures:
These vulnerabilities will persist for a while so it better to know the safety measures. One basic safety measure is to run the command “no vstack config” on the affected device. If that option isn’t available, the best option would be to restrict access via an access control list for the interface.
It has been confirmed that devices in India are prone to these attacks so it may be beneficial to know how to deal with these vulnerabilities.
In conclusion, the best way to prevent such vulnerabilities is to implement vulnerability management solutions to detect and fix in real-time such threats caused by device software issues.