REvil is an ambitious criminal ransomware-as-a-service (RAAS) enterprise that first came to prominence in April 2019. The REvil group is also known sometimes by other names such as Sodin and Sodinokibi. It has emerged as one of the world’s most notorious ransomware operators. In just the past month, it extracted an $11 million payment from the world’s largest meatpacking company, demanded $5 million from a Brazilian medical diagnostics company, and launched a large-scale attack on dozens, perhaps hundreds, of companies that use IT management software from Kaseya VSA.

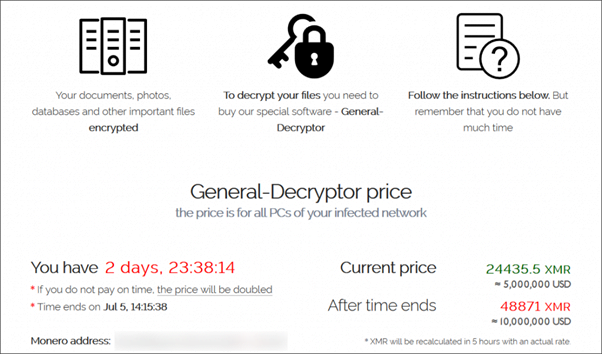
REvil has gained a reputation for attempting to extort far larger payments from its corporate victims than that typically seen in other attacks. It is actively promoted underground cybercrime forums as the best choice for attacking business networks where there is more money to be made than infecting home users’ computers.
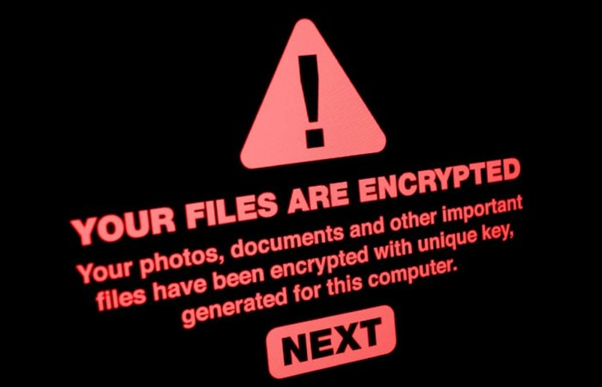
Aside from the many high-profile companies and organizations who have fallen foul of REvil, it is stealing data from the computers and networks of its victims before they are encrypted. This is a technique of applying additional pressure on victims which is becoming more and more commonplace.

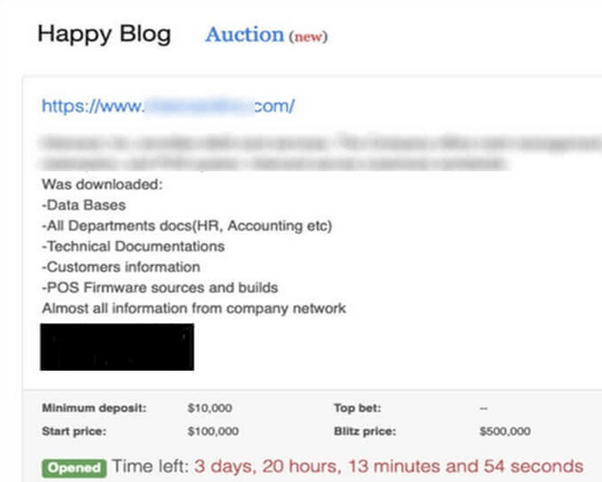
If the ransom isn’t paid in the provided time REvil threatens to release the stolen data by auctioning it on its own website “Happy Blog”.
The “Happy Blog” lists recent victims of REvil, attaching a sample of the stolen data as proof that information has been exfiltrated from an organization. The REvil gang even offers a “trial” decryption to prove to the victim that their files can be decrypted.
A countdown timer indicates when data leaks will be made public, applying more pressure to companies debating how they should respond.
Restoring Data
Although the firm could restore their data from a secure backup and can get the site up and running. But the catch here is that the criminals still have the company’s data. The data can be sold to someone on the dark web and could leak some sensitive information about the firm, and even if the hackers are unable to sell the data, still incalculable damage can be done to an organization’s brand and business relationships.
Ransomware-as-a-Service(RAAS)
REvil is one of the most prominent providers of ransomware as a service (RaaS). This criminal group provides adaptable encryptors and decryptors, infrastructure and services for negotiation communications, and a leak site for publishing stolen data when victims don’t pay the ransom demand. For these services, REvil takes a percentage of the negotiated ransom price as their fee. Affiliates of REvil often use two approaches to persuade victims into paying up: They encrypt data so that organizations cannot access information, use critical computer systems or restore from backups, and they also steal data and threaten to post it on a leak site a tactic known as double extortion.
How does REvil ransomware infect one’s organization?
There are a variety of methods an attacker could use to plant the malware. These include exploiting a vulnerability to gain access to a computer on your company’s network, spear-phishing, or exploiting a third-party business partner.
In some cases, the attack may actually come from a client or partner who has already fallen victim to the hackers.
Paying ransom or not
This ultimately is a decision that only the firm can make. One needs to bear in mind that the more companies that pay a ransom, the more likely it is that criminals will launch similar attacks in the future. At the same time, firms may feel that their business needs to make the difficult but pragmatic decision to pay the criminals if it feels that there is no other way around. Informing law enforcement agencies about the incident and work with them to help them investigate who might be behind the attacks.
Either be it is a firm or an individual person, one should always keep one thing in mind: paying the ransom does not necessarily mean you have erased the security problems that allowed you to be infected in the first place. If you don’t find out what went wrong and why and fix it, then you could easily fall victim to further cybercrime attacks in the future.
Prevention
- The company should be making secure offsite backups.
- Employees should be running up-to-date security solutions and ensuring that their computers are protected with the latest patches against newly-discovered vulnerabilities.
- Hard-to-crack, unique passwords should be used to protect sensitive data and accounts as well as enabling multi-factor authentication.
- The company should be encrypting your sensitive data wherever possible.
- Educating and informing staff about risks and the methods used by cybercriminals to electronically infiltrate organizations.